SIEM Solutions Splunk vs ArcSight
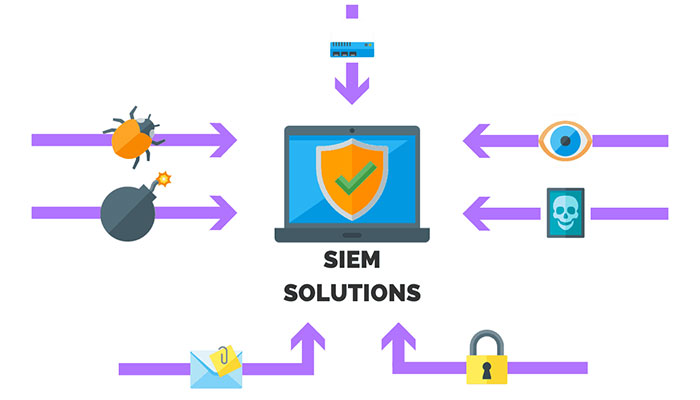
Security information and event management (SIEM) has evolved with advanced analytics such as user behavior analysis (UBA), network flow insights, and artificial intelligence (AI) to accelerate discovery. It also integrates seamlessly with Security, Automation, and Response (SOAR) orchestration platforms for incident response and remediation. SIEM can be enhanced through consulting and managed services to expand threat management programs, policy management, and security personnel.
What is Splunk?
Splunk license is a SIEM that is installed and operates as a powerful platform to collect logs, search, view, analyze and analyze data in organizations. In this solution, information discovery is done by processing thousands of data from checking logs.
In addition, by Splunk, all the collected data can be used and exploited in the best way, and it is also possible to put the organization at a higher level of performance, competition, profitability and security by creating a level of operational intelligence. SIEM is a new technology that is used for the security of organizations in order to prevent the attacks of hackers and malicious malware.
The main purpose of SIEM is to centralize logs, report and manage them. Today, many companies offer this product in different architectures, one of the best companies in the field of SIEM is SPLUNK.
The necessity of using SPLUNK as a SIEM
Without checking and analyzing the recorded logs, it is not possible to detect the occurrence of an attack. Logs are the only way to identify attackers. Even if the organization is informed of the attack, without comprehensive logs that have not been manipulated by the attackers, the organization will not have any insight into the details of the attack.
Today, by using a centralized system in order to receive, collect and structure these events, it can help a lot in quick analysis and making logical connections between these reported events.
Splunk key features
- Scalability and agility
- High speed data processing
- Threat analysis and threat response
- Splunk license and activation (Splunk License)
- High level of compatibility with different data
- Rapid detection of threats in a fraction of a second
- It has a security system based on intelligent analysis
- The purchase cost is much lower than other competitors
- Increasing the effectiveness of SOC processes and personnel
- Quickly adapt data to changes in threats and face advanced threats
- Empower your SOC with a fast and flexible security intelligence platform
- Instant detection, investigation and reporting in cases of fraud and abuse
- Intelligent extraction of fields and quick data recovery, possibility to identify fields
- The ability to implement in the form of Cloud, On-Premise and a combination of these two modes
- Various reports (in various formats and various charts) and the possibility of display in user dashboards
- The Splunk license considers the volume of incoming logs in 24 hours. Up to a limit to send your equipment logs to
- Do not have a SIEM service. (The license of other products is usually based on the number of logs produced per second (EPS))
- real-time search, time period search, etc.) and display the search results in the form of various reports, graphs and dashboards
- The possibility of various search methods (logical searches, the possibility of string searches, the use of wildcards in the search parameters.
- Monitoring and warning and scheduling these warnings and managing the display of warnings (sending emails, executing scripts or displaying warnings, etc.)
- Scalability (the possibility of using Splunk at the level of organizations and small and medium-sized companies to large organizations is one of its capabilities.)
- There is a free two-month trial version that can be downloaded and installed from Splank’s website. None of the competing products, including HP ArcSight and IBM Qradar, have such a possibility.
What is ArcSight?
HP’s ArcSight is a reliable product that has been widely implemented worldwide. ArcSight brings a centralized security monitoring platform to the organization. This company helps to implement SOC in the organization by providing an integrated product set to collect and evaluate security and risk information.
As mentioned, security events are generated at the lowest level by event generation resources such as network tools, security tools, access control, and such resources, and are collected and normalized and then integrated by system connectors. Then, these series of events in the form of logs and alerts at a higher level are entered into the correlation and clustering process by modules such as ArcSight logger or ArcSight ESM to check the existence of connections between alerts and different stages of the attack. At this stage, statistical information is also taken from the set of events and presented to the system administrator in the form of multiple reports at different levels.
ArcSight key features
- It has Logger, Express and ESM models
- Network configuration management and correction of its defects
- Applying IT policies to allocate network and bandwidth resources
- Monitoring users in order to identify and prevent unusual and threatening activities
- Creation of accurate, flexible reports in different formats required by the organization
- Collecting and aggregating logs from all IT resources of the organization (network, security and servers)
- Identifying and quickly fixing important and risky security vulnerabilities in the organization’s services and web applications
- Management of millions of events and security information in order to obtain comprehensive and in-depth information about threat activities
- Updated and supported by the most skilled experts in DVLabs, ArcSight, Fortify and HP Labs teams