Cisco Stealthwatch Learning Network License Virtual Service Installation Guide
Managing and Licensing Agents
After you run the install script, you can register Cisco Stealthwatch Smart Licensing on your controller, then enable the managed agents.
Smart Licensing Overview
To deploy the Learning Network License, you must register your controller with Cisco Smart Licensing. If you do not, your deployment enters Evaluation Mode, a 90-day trial which limits you to a maximum of 10 managed agents, and disables new functionality when the 90 days expire.
Cisco Smart Licensing lets you purchase and manage a pool of licenses centrally. Unlike product authorization key (PAK) licenses, Smart Licenses are not tied to a specific serial number or license key. Smart Licensing lets you assess your license usage and needs at a glance.
In addition, Smart Licensing does not prevent you from deploying agents. You can deploy an agent and purchase the license later. This allows you to deploy and use an agent, and avoid delays due to purchase order approval.
Smart Software Manager
When you purchase one or more Smart Licenses, you manage them in the Cisco Smart Software Manager: http://www.cisco.com/web/ordering/smart-software-manager/index.html. The Smart Software Manager lets you create a master account for your organization.
By default, your licenses are assigned to the Default Virtual Account under your master account. As the account administrator, you can create additional virtual accounts; for example, for regions, departments, or subsidiaries. Multiple virtual accounts help you manage large numbers of licenses and appliances.
You manage licenses and appliances by virtual account. Only that virtual account’s appliances can use the licenses assigned to the account. If you need additional licenses, you can transfer an unused license from another virtual account. You can also transfer appliances between virtual accounts.
For each virtual account, you can create a Product Instance Registration Token. Enter this token ID when you register a controller. You can create a new token if an existing token expires. An expired token does not affect a registered controller that used this token for registration, but you cannot use an expired token to register a controller. Also, a registered controller becomes associated with a virtual account based on the token you use. You can also create a new token, and use it to reregister even if the current token is still valid.
Smart License Types
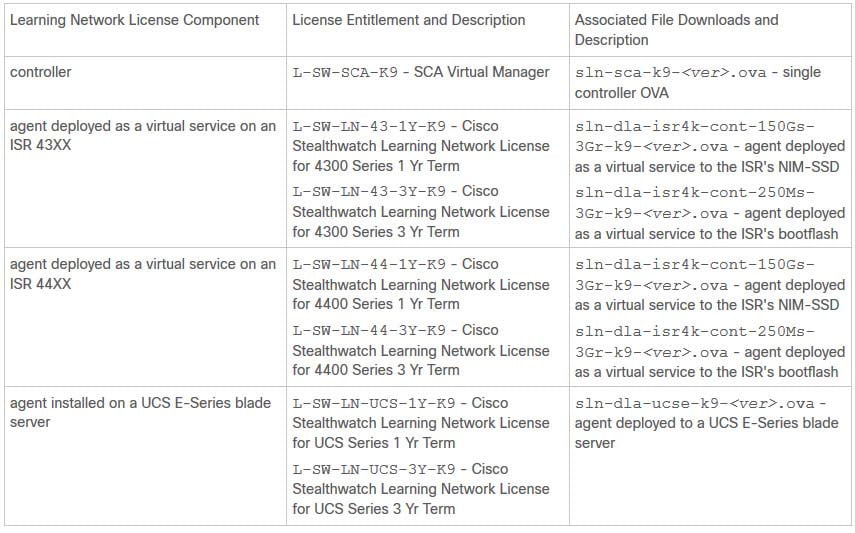
Each Learning Network License component has a corresponding license entitlement, as described in the following table:
Table 1 Smart License Entitlement Types
You must obtain one license entitlement for each controller and agent deployed to your environment.
The controller web UI displays license entitlement counts for your agents. When you enable a managed agent with the controller, the Smart Licensing Agent automatically requests a license entitlement for that agent, specific to that installation type. It also updates the license count. Similarly, when you disable a managed agent from the controller, the Smart Licensing Agent requests to free the license entitlement, and updates the license count.
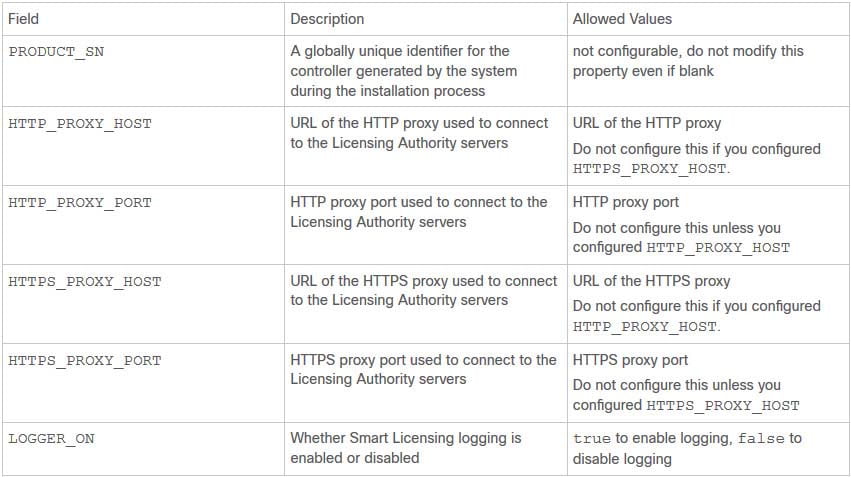
By default, the controller connects directly to the Licensing Authority servers. You can configure the sa.properties Smart Licensing configuration file to connect to the Licensing Authority servers through an HTTP or HTTPS proxy server.
Smart Licensing Configuration
By default, the controller logs information about Smart Licensing. You can disable this in the sa.properties configuration file.
Smart Licensing Configuration File Settings
If you want to change how your controller connects to the Licensing Authority servers, you can configure an HTTP proxy or HTTPS proxy. You cannot configure more than one.
Table 2 sa.properties Configuration File Settings
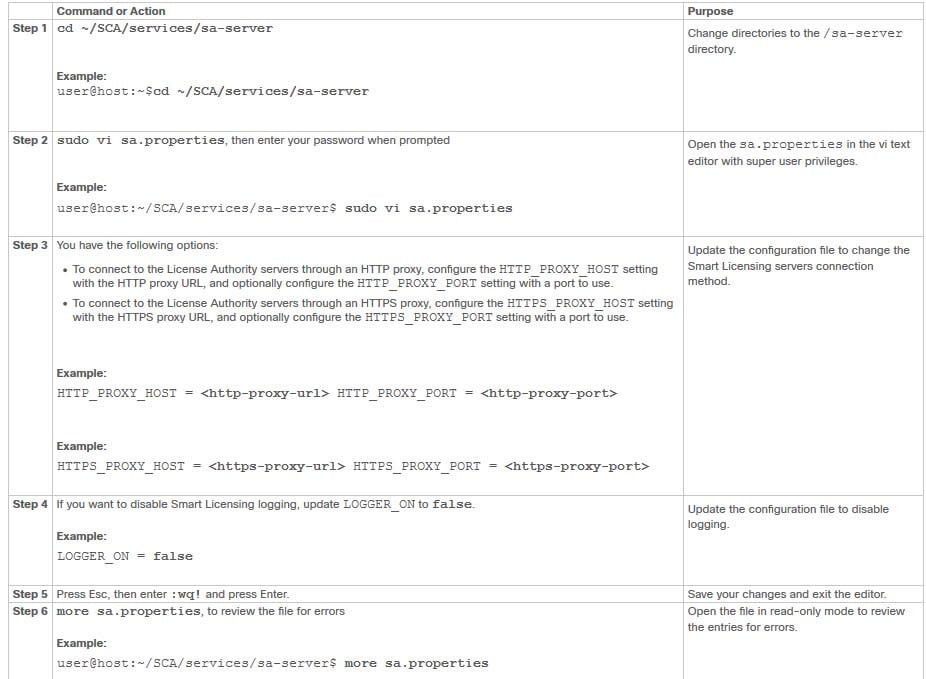
Updating the Smart Licensing Configuration File
Before You Begin
- Log into the controller VM console.
SUMMARY STEPS
1. cd ~/SCA/services/sa-server
2. sudo vi sa.properties, then enter your password when prompted
3. You have the following options:
- To connect to the License Authority servers through an HTTP proxy, configure the HTTP_PROXY_HOST setting with the HTTP proxy URL, and optionally configure the HTTP_PROXY_PORT setting with a port to use.
- To connect to the License Authority servers through an HTTPS proxy, configure the HTTPS_PROXY_HOST setting with the HTTPS proxy URL, and optionally configure the HTTPS_PROXY_PORT setting with a port to use.
4. If you want to disable Smart Licensing logging, update LOGGER_ON to false.
5. Press Esc, then enter :wq! and press Enter.
6. more sa.properties, to review the file for errors
DETAILED STEPS
What to Do Next
- Restart the controller processes, as described in the next section.
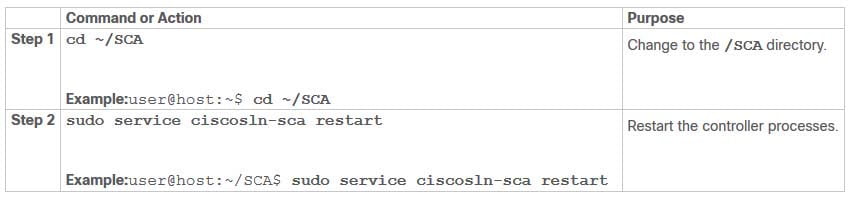
Restarting the Controller Processes
SUMMARY STEPS
1. cd ~/SCA
2. sudo service ciscosln-sca restart
DETAILED STEPS
Logging into the Controller Web UI
When you installed the controller, you defined an IP address for the controller web UI, and reset the administrator user account (admin) password. Log in with the temporary password printed to the controller VM console. After you log in once, you must change the password and confirm the new password.
In your web browser, navigate to https://controller-web-ip-address, then enter your controller web username and password when prompted.
Registering the Controller Instance
Before You Begin
- Obtain a registration token from the Smart Software Manager (https://www.cisco.com/c/en/us/buy/smart-accounts/software-manager.html).
- Log into the controller web UI.
Step 1 Select Dashboard.
Step 2 Click Smart Licensing.
Step 3 Click Register.
Step 4 Paste your registration token into the Smart Software Licensing Product Registration field.
Step 5 If you want to use a registration token and the current token is still valid, check Reregister this product instance if it is already registered.
Step 6 Click Register.