Home » Security License » GFI » Security » Mail Essential
The licensed GFI MailEssentials is a comprehensive email security platform that provides organizations with a wide range of features and capabilities to protect their email systems from spam, phishing, malware, and other threats. The platform is designed to be easy to use and highly customizable, enabling organizations to tailor their email security strategies to their specific needs.
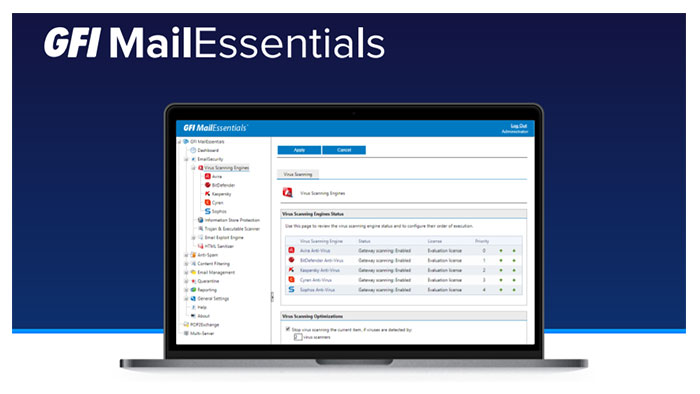
The licensed GFI MailEssentials is an email security platform that is designed to protect organizations from a wide range of email-based threats. The platform provides a range of features and capabilities, including anti-spam and anti-phishing protection, email content filtering and data leakage prevention, email archiving and compliance, and advanced threat protection.
GFI MailEssential is licensed on a per-user basis, with pricing based on the number of users and the desired feature set. The platform is available in two editions: Standard Edition and Premium Edition.
The Standard Edition provides anti-spam and anti-phishing protection, email content filtering and data leakage prevention, and email archiving and compliance capabilities. The Premium Edition includes all of the features of the Standard Edition, as well as advanced threat protection capabilities, including sandboxing and URL protection.
Both editions of GFI MailEssentials are available as perpetual licenses, which provide access to the software indefinitely, or as subscription licenses, which provide access to the software for a specified period of time (usually one year).
The licensed GFI MailEssential licenses can be purchased directly from GFI Software or from authorized resellers. The cost of licensing varies depending on the number of users and the desired feature set, as well as any applicable discounts or promotions.
It’s worth noting that GFI MailEssentials licenses are not transferable between organizations. This means that if an organization purchases a GFI MailEssentials license and later decides to transfer ownership of the license to another organization, they will need to purchase a new license for the new organization.
In summary, GFI MailEssentials is licensed on a per-user basis, with pricing based on the number of users and the desired feature set. The platform is available in two editions: Standard Edition and Premium Edition, and licenses can be purchased as perpetual licenses or subscription licenses. GFI MailEssentials licenses are not transferable between organizations.
For more information you can see all GFI License products
One of the key advantages of GFI MailEssentials is its anti-spam and anti-phishing protection capabilities. The platform uses a range of techniques to identify and block spam and phishing emails, including content filtering, sender reputation analysis, and machine learning algorithms.
The licensed GFI MailEssential also provides administrators with granular control over their anti-spam and anti-phishing strategies, enabling them to tailor their policies to their specific needs. This can help organizations to reduce the volume of spam and phishing emails that reach their users, improving productivity and reducing the risk of cyber attacks.
GFI MailEssentials also provides email content filtering and data leakage prevention capabilities, which are critical for protecting sensitive information and intellectual property. The platform enables administrators to create policies that block or quarantine emails containing specific types of content, such as credit card numbers, social security numbers, or other sensitive information.
The platform also provides data leakage prevention capabilities, which enable organizations to monitor outbound email traffic for potential data breaches. This can help organizations to identify and prevent data exfiltration, reducing the risk of data loss and regulatory noncompliance.
The licensed GFI MailEssentials also provides email archiving and compliance capabilities, which are critical for organizations that need to comply with industry regulations or legal requirements. The platform enables organizations to archive all inbound and outbound emails, providing a complete record of all email communications.
This can help organizations to meet their compliance requirements and provide evidence in the event of a legal challenge. GFI MailEssentials also provides granular control over email retention policies, enabling organizations to retain emails for as long as necessary to meet their specific needs.
For more information, GFI Security
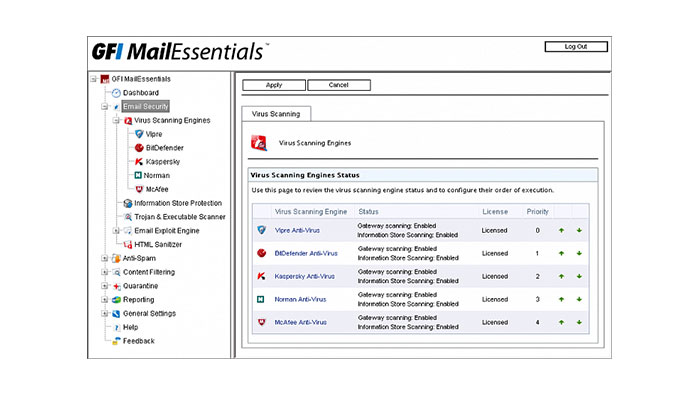
Finally, GFI MailEssentials provides advanced threat protection capabilities, which are critical for protecting organizations from the latest email-based threats. The platform uses machine learning algorithms and other advanced techniques to identify and block malware, ransomware, and other advanced threats.
The licensed GFI MailEssentials also provides sandboxing capabilities, which enable organizations to safely detonate suspicious email attachments in a controlled environment. This can help organizations to identify and block new and emerging threats, reducing the risk of data loss and business disruption.
GFI MailEssentials has been deployed by a wide range of organizations, across a variety of industries and use cases. For example, a leading healthcare provider in the United States deployed GFI MailEssentials to protect its email systems from spam and phishing attacks. The platform’s anti-spam and anti-phishing protection capabilities enabled the organization to reduce the volume of unwanted emails its employees received, improving productivity and reducing the risk of cyber attacks.
Another example is a major financial services company that deployed GFI MailEssentials to improve its email archiving and compliance capabilities. The platform’s email archiving and retention policies enabled the company to meet its regulatory requirements, while also providing a complete record of all email communications for legal and business purposes.
GFI MailEssentials is a comprehensive email security platform that provides organizations with a wide range of features and capabilities to protect their email systems from spam, phishing, malware, and other threats. The platform’s anti-spam and anti-phishing protection, email content filtering and data leakage prevention, email archiving and compliance, and advanced threat protection capabilities make it a powerful tool for organizations looking to improve their email security posture.
Real-world examples of GFI MailEssentials deployments demonstrate the platform’s ability to improve productivity, reduce the risk of cyber attacks, and meet regulatory and legal requirements. If you’re considering GFI MailEssentials for your organization’s email security needs, it’s worth exploring the platform’s capabilities and features in detail. With its powerful anti-spam and anti-phishing protection, email content filtering and data leakage prevention, email archiving and compliance, and advanced threat protection capabilities, GFI MailEssentials can help organizations to protect their email system from a wide range of threats, improving their overall security posture.
"*" indicates required fields