Network Configuration Manager (NCM)
Home » Network License » SolarWinds » Network Management » Network Configuration Manager (NCM)
In today’s rapidly evolving digital landscape, efficient network management is pivotal to an organization’s success. SolarWinds Network Automation Manager (NAM) emerges as a powerful solution designed to streamline network operations, enhance performance, and minimize downtime. This article delves into the intricate features, use cases, and licensing options of SolarWinds NAM, offering valuable insights for IT professionals seeking advanced network automation solutions.
Understanding Network Automation
What is network automation?
Network automation is the practice of using software and technology to automate manual network management tasks. This includes activities like device configuration, network monitoring, and troubleshooting. SolarWinds NAM takes network automation to the next level by providing a comprehensive suite of tools for both real-time monitoring and automation.
The role of automation in network management
Automation is essential for modern network management due to the increasing complexity of networks. It reduces the risk of human error, speeds up processes, and ensures network stability. SolarWinds NAM leverages automation to simplify routine tasks, allowing IT teams to focus on strategic initiatives.
Key Features of SolarWinds NAM
Real-Time Network Monitoring
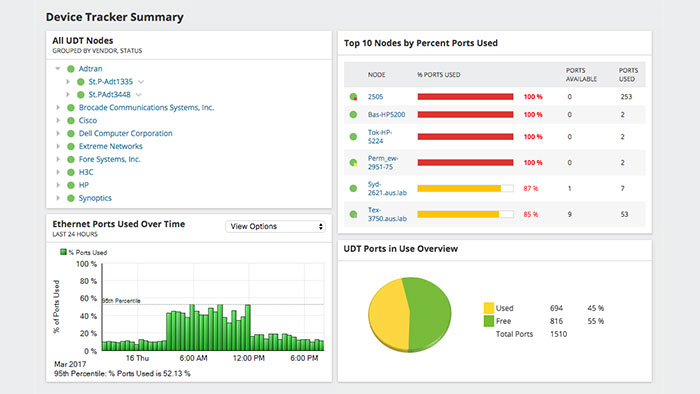
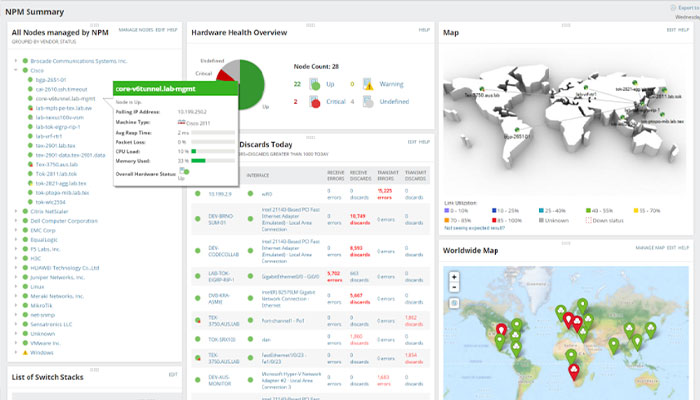
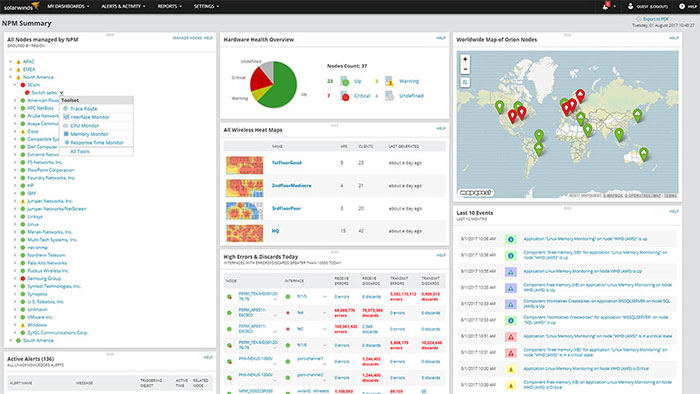
SolarWinds NAM offers real-time visibility into network performance. It provides insights into bandwidth utilization, traffic patterns, and device status, enabling administrators to identify and address issues proactively. The real-time monitoring feature includes customizable dashboards, alerts, and reports for a comprehensive view of the network.
Network Configuration Management
Managing network configurations can be a daunting task. SolarWinds NAM simplifies this process by automating configuration backups, changes, and compliance checks. It ensures that network devices are configured correctly and consistently, reducing the risk of configuration-related outages.
Automated Network Discovery
Network discovery is the foundation of effective network management. SolarWinds NAM automates the discovery of devices, interfaces, and dependencies within your network. This automated approach ensures that your network documentation is always up-to-date, which is crucial for troubleshooting and planning.
Performance Optimization with SolarWinds NAM
SolarWinds NAM doesn’t just monitor your network; it optimizes it. By analyzing performance data, NAM can identify areas where improvements are needed. It helps IT teams make data-driven decisions to enhance network efficiency and user experience.
Use Cases for SolarWinds NAM
Enterprise Networks
Large enterprises with complex network infrastructures can benefit significantly from SolarWinds NAM. It provides the scalability and automation needed to manage vast networks efficiently. NAM’s real-time monitoring is invaluable for ensuring high availability and performance.
Service Providers
Telecommunication and service providers often operate extensive networks that serve countless customers. SolarWinds NAM aids these providers in maintaining service quality, managing network resources, and rapidly responding to issues.
Data Centers
Data center networks must be highly reliable. SolarWinds NAM helps data center administrators monitor and optimize network performance to ensure that critical applications and services remain accessible.
License Models and Pricing
SolarWinds offers flexible licensing options for NAM to accommodate various organizational needs. Licensing typically depends on factors like the number of devices, interfaces, or nodes in your network. SolarWinds NAM’s modular approach allows organizations to choose the features and capacity that best suit their requirements, making it a cost-effective solution for businesses of all sizes.
Installation and Setup
Deploying SolarWinds NAM is a straightforward process. SolarWinds provides detailed installation guides and documentation to assist users through every step of the setup. The software is designed to be user-friendly, allowing even non-experts to get it up and running quickly.
Integration with Other SolarWinds Products
SolarWinds NAM seamlessly integrates with other SolarWinds products, creating a comprehensive network management ecosystem. Integration with tools like SolarWinds Network Performance Monitor (NPM) and SolarWinds Network Configuration Manager (NCM) enhances visibility and control over your network infrastructure.
Best Practices for Using SolarWinds NAM
To make the most of SolarWinds NAM, consider the following best practices:
- Regularly review and fine-tune alerting thresholds to avoid false alarms.
- Implement automated workflows for common network tasks.
- Train your IT team to leverage NAM effectively.
- Stay updated with SolarWinds NAM updates and patches.
- Security and Compliance with SolarWinds NAM
SolarWinds NAM contributes to network security and compliance by providing features like configuration management and change tracking. It helps organizations meet industry-specific compliance standards such as HIPAA, PCI DSS, or GDPR by ensuring network configurations adhere to regulatory requirements.
How SolarWinds NAM Will Help IT and Network Administrators?
SolarWinds Network Automation Manager (NAM) offers a wide array of features and capabilities that can significantly benefit IT and network administrators. Here’s how SolarWinds NAM can help these professionals:
Streamlined Network Management
SolarWinds NAM simplifies routine network management tasks, such as device configuration and network discovery. This allows administrators to save time and focus on more strategic aspects of network operations.
Real-Time Monitoring and Visibility
NAM provides real-time visibility into network performance, including bandwidth utilization, traffic patterns, and device status. Administrators can quickly identify issues, troubleshoot problems, and ensure optimal network performance.
Proactive Issue Identification
With proactive alerts and customizable dashboards, NAM enables administrators to identify and address network issues before they impact users. This proactive approach minimizes downtime and improves overall network reliability.
Efficient Network Configuration Management
NAM automates network configuration backups, changes, and compliance checks. Administrators can ensure that network devices are configured correctly and consistently, reducing the risk of configuration-related outages.
Automated Network Discovery
Network discovery is automated with NAM, ensuring that the network documentation is always up-to-date. This is crucial for troubleshooting, planning, and maintaining a reliable network inventory.
Optimized Network Performance
SolarWinds NAM doesn’t just monitor the network; it also analyzes performance data to identify areas for improvement. Administrators can make data-driven decisions to enhance network efficiency and user experience.
Scalability for Enterprise Networks
Large enterprises with complex network infrastructures can benefit from NAM’s scalability and automation capabilities. It can handle vast networks and provide the necessary tools for efficient management.
Service Quality Assurance for Providers
Telecommunication and service providers rely on NAM to maintain service quality, manage network resources, and respond rapidly to issues. This ensures customer satisfaction and minimizes service disruptions.
Reliable Data Center Management
Data center administrators use NAM to monitor and optimize network performance, ensuring that critical applications and services remain accessible and reliable.
Cost-Effective Licensing
SolarWinds offers flexible licensing options for NAM, making it accessible to organizations of all sizes. Administrators can choose the features and capacity that best suit their requirements, ensuring cost-effectiveness.
Integration with Other Tools
NAM seamlessly integrates with other SolarWinds products, creating a unified network management ecosystem. This integration enhances visibility and control over the entire network infrastructure.
Enhanced Security and Compliance
NAM contributes to network security and compliance by providing features like configuration management and change tracking. It helps organizations meet industry-specific compliance standards by ensuring network configurations adhere to regulatory requirements.
Automation for Routine Tasks
SolarWinds NAM allows administrators to automate repetitive tasks, reducing the risk of human error and freeing up time for more strategic initiatives.
Improved Troubleshooting
NAM’s real-time monitoring and network documentation capabilities make troubleshooting more efficient. Administrators can quickly identify the root causes of issues and take corrective actions.
Data-Driven Decision-Making
By providing comprehensive network performance data and insights, NAM empowers administrators to make informed decisions that drive network optimization and efficiency.
In summary, SolarWinds NAM empowers IT and network administrators by automating tasks, enhancing visibility, improving network performance, and providing the tools needed to manage networks of all sizes effectively. It helps reduce downtime, enhance security, and streamline network operations, ultimately contributing to the success of organizations in today’s interconnected digital landscape.
Conclusion: Empowering Your Network Management
In conclusion, SolarWinds NAM is a robust network automation solution that offers real-time monitoring, configuration management, and automation capabilities. Its versatility makes it suitable for a wide range of industries and network sizes. By implementing SolarWinds NAM, organizations can enhance network efficiency, reduce downtime, and ensure a stable and secure network environment.