Wallix
Home » Security License » Wallix
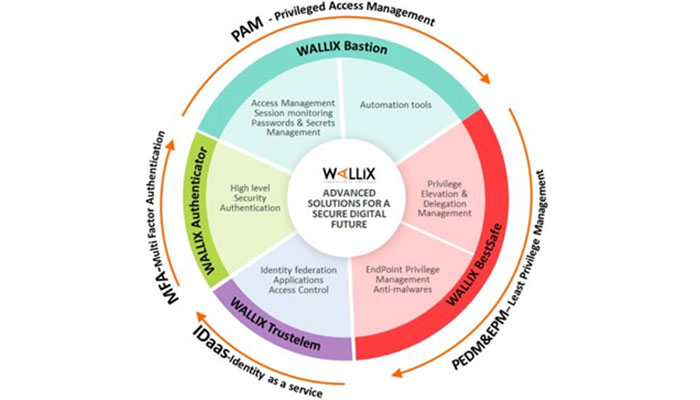
Wallix is a cybersecurity company that specializes in Privileged Access Management (PAM) solutions. Their networking products are designed to help businesses of all sizes protect their sensitive data and prevent cyber attacks. With a focus on innovation and simplicity, Wallix has become a trusted name in the cybersecurity industry.
The Importance of Network Security: Why Businesses Need Wallix
Network security is a critical concern for businesses of all sizes. Cyberattacks are becoming more sophisticated every day, and even small businesses are at risk of being targeted. In fact, a recent study found that 43% of cyberattacks target small businesses.
One of the most significant threats to network security is the unauthorized access of privileged accounts. Privileged accounts are those that have access to sensitive data or critical systems, and they are often targeted by cybercriminals. If an attacker gains access to a privileged account, they can wreak havoc on a business’s network, steal sensitive data, and cause significant financial losses.
This is where Wallix comes in. Their network products are designed to help businesses protect their privileged accounts by providing secure access control, password management, and session recording. With Wallix, businesses can rest assured that their sensitive data is protected from malicious actors.
Understanding Wallix Network Products
Wallix offers a range of network products, each designed to help businesses protect their privileged accounts and prevent cyberattacks. Here is an overview of their product offerings:
Wallix Bastion
This is Wallix’s licensed flagship PAM solution. It provides secure access control, password management, and session recording for privileged accounts. It also includes features like multi-factor authentication and risk analysis to help businesses stay secure.
Key features of Wallix Bastion
Here are some of the key features of Wallix Bastion:
- Secure Access Control: The licensed Wallix Bastion provides granular access control for privileged accounts, allowing businesses to restrict access to sensitive data and systems. This includes fine-grained access controls based on roles and permissions, as well as multi-factor authentication for added security.
- Password Management: The licensed Wallix Bastion includes a password management feature that allows businesses to generate, store, and rotate passwords for privileged accounts. This helps ensure that passwords are strong and that they are changed frequently to prevent unauthorized access.
- Session Recording: The licensed Wallix Bastion provides session recording for privileged accounts, allowing businesses to monitor all activity and detect any suspicious behavior. Session recordings can be used as audit logs for compliance purposes, as well as for forensic analysis in the event of a security incident.
- Risk Analysis: The licensed Wallix Bastion includes a risk analysis feature that helps businesses identify potential vulnerabilities and threats in their network. This feature uses machine learning algorithms to analyze user behavior and identify anomalies or suspicious activity.
- Compliance: Wallix Bastion is designed to help businesses meet compliance requirements for regulations like PCI-DSS, HIPAA, and GDPR. It includes features like session recording and access controls that help businesses demonstrate compliance with these regulations.
Wallix Bastion is designed to be easy to use and scalable, making it a good fit for businesses of all sizes. It includes an intuitive user interface and can be deployed on-premises or in the cloud. Additionally, it integrates with other Wallix products, like DataPeps and AdminBastion, for a more comprehensive network security solution.
Overall, Wallix Bastion is a robust and comprehensive PAM solution that provides businesses with the tools they need to protect their privileged accounts and sensitive data from cyberattacks and data breaches.
Wallix AdminBastion
This product is designed for businesses that need to manage multiple Wallix Bastion instances. It provides centralized management and monitoring of multiple Bastion instances, making it easier for businesses to stay on top of their network security.
Wallix DataPeps
This product is a secure file sharing solution that allows businesses to share files securely with customers and partners. It includes features like end-to-end encryption and access control to ensure that only authorized users can access sensitive files.
Wallix CloudBastion
This product is a cloud-based PAM solution that provides secure access control and password management for privileged accounts in the cloud. It is designed to integrate seamlessly with cloud infrastructure providers like AWS and Azure.
Wallix’s DataPeps vs other secure file sharing solutions on the market
Wallix’s DataPeps product is a secure file sharing solution that allows businesses to share files securely with customers and partners. It includes features like end-to-end encryption and access control to ensure that only authorized users can access sensitive files. But how does it compare to other secure file sharing solutions on the market?
One of the most well-known secure file sharing solutions on the market is Dropbox. Dropbox is a cloud-based file sharing solution that provides encrypted storage and file synchronization across devices. While Dropbox is widely used and well-regarded for its ease of use and flexibility, it has limitations when it comes to security.
Dropbox’s encryption is not end-to-end, meaning that while files are encrypted in transit and at rest, they can still be accessed by Dropbox employees. This is a concern for businesses that need to protect sensitive data. Additionally, Dropbox’s access controls are limited, making it difficult to restrict access to sensitive files.
Another secure file sharing solution on the market is Box. Box is a cloud-based file sharing solution that provides advanced security features like encryption, access controls, and audit trails. Box is often used by businesses in regulated industries like healthcare and finance.
Compared to Dropbox, Box offers advanced security features like granular access controls and file-level encryption. However, Box’s pricing can be steep, making it less accessible to small businesses.
When it comes to secure file sharing, Wallix’s DataPeps product stands out for its end-to-end encryption and granular access controls. With DataPeps, businesses can be sure that only authorized users can access sensitive files, and that those files are encrypted from end to end. DataPeps also provides audit trails and activity logs, making it easy to monitor file access and usage.
In terms of pricing, DataPeps is competitively priced, making it accessible to businesses of all sizes. Additionally, DataPeps is designed to integrate with other Wallix products, making it easy to implement as part of a larger network security strategy.
While Dropbox and Box are well-known names in the secure file sharing market, they do have limitations when it comes to security and pricing. Wallix’s DataPeps product offers end-to-end encryption and granular access controls at a competitive price, making it a strong contender for businesses serious about protecting their sensitive data.
Use Cases for Wallix Network Security: How Wallix Helps Businesses Stay Secure
Wallix’s licensed network products are used by businesses in a wide range of industries to protect their sensitive data and prevent cyberattacks. Here are some examples of how Wallix helps businesses stay secure:
- Finance: Financial institutions are a prime target for cybercriminals. Wallix’s PAM solutions help these businesses protect their privileged accounts and prevent data breaches.
- Healthcare: Healthcare organizations are responsible for protecting sensitive patient data. Wallix’s PAM solutions help these organizations meet compliance requirements and prevent data breaches.
- Government: Government agencies are responsible for protecting sensitive data like classified information. Wallix’s PAM solutions help these agencies meet security requirements and prevent data breaches.
- Retail: Retailers must protect customer payment information and other sensitive data. Wallix’s PAM solutions help these businesses prevent data breaches and maintain PCI compliance.
Wallix Licensing: A Guide to Their Licensing Model and How It Works
Wallix’s licensing model is designed to be flexible and scalable to meet the needs of businesses of all sizes. Here is a breakdown of their licensing options:
- Perpetual License: This is a traditional software license that allows businesses to use Wallix’s products indefinitely. It includes maintenance and support for the first year, with additional support available for an additional fee.
- Subscription License: This is a subscription-based license that allows businesses to use Wallix’s products for a set period of time, usually one or three years. It includes maintenance and support for the duration of the subscription.
- SaaS License: This is a cloud-based license that allows businesses to use Wallix’s products on a subscription basis. It includes maintenance and support, as well as automatic updates and upgrades.
Real-World Examples of How Wallix Helps Businesses
Here are some real-world examples of how Wallix has helped businesses stay secure:
A large financial institution was struggling to manage its privileged accounts across multiple systems. With Wallix Bastion, the institution was able to centralize its privileged account management and improve its overall network security.
A healthcare organization was concerned about the security of its sensitive patient data. With Wallix Bastion, the organization was able to implement secure access control and password management for its privileged accounts, ensuring that only authorized users could access sensitive data.
A government agency needed tomeet strict security requirements for classified information. With Wallix Bastion, the agency was able to implement fine-grained access control and session recording for its privileged accounts, ensuring that all activity was monitored and audited.
The Future of Network Security and How Wallix is Leading the Way
As cyberattacks become more sophisticated, businesses must stay ahead of the curve when it comes to network security. Wallix is leading the way in this regard, with a focus on innovation and simplicity. They are constantly updating their products to stay ahead of the latest threats, and they are committed to providing their customers with the best possible experience.
Wallix’s network products are designed to be easy to use, with intuitive interfaces and powerful features. This makes it easier for businesses of all sizes to protect their privileged accounts and prevent cyberattacks.
Conclusion: Why Wallix is a Smart Choice for Businesses Serious About Security
In conclusion, Wallix is a smart choice for businesses that take network security seriously. With their range of PAM solutions, businesses can protect their privileged accounts and prevent cyberattacks. Their licensing options are flexible and scalable, making it easy for businesses of all sizes to implement their products. And with a focus on innovation and simplicity, Wallix is leading the way when it comes to network security.